There are thousands of technical terms are used for computer security, many of them are bit hard to explain in simple words, that’s why they are often used incorrectly. When it comes to Virus, malware, worm, etc. a non-tech savvy person refers them as a virus. I get lots of such comments, messages and requests on my YouTube channel where people refer everything as virus whether it is a Virus, trojan, spyware, adware or even an unknown software. Sometimes you may get pop up on various Websites that your computer is infected with Virus, and you need to scan your computer, but that is not true, such pop-ups during web browsings are ads running by different advertisers, and they want to sell their product by scaring you.
What is the difference: Virus, Malware, Trojan, Worm, Spyware, etc.
So how much do you know about Virus, Malware, Trojan, Worms, Rootkit, Adware, Ransomware, Exploit, etc? In this detailed article, I will discuss the difference between a virus, malware, trojan, etc. which will help you to find the correct solution for your computer problems.
So let’s get started.
What is Malware?
The word Malware is used for malicious software and is a general term for Virus, worm, trojan, rootkit, spyware and nearly everything which is specifically designed to harm your computer and steal information. Malware does not include buggy software, programs you don’t like, software which crashes a lot but software which are specifically created to harm our PC.
Virus
The most common word used for any bad software, however, we use the term “malware” now. A virus is a program which can self-replicate itself after infecting a computer, it attach itself to other programs and get installed while installing the genuine software. After the execution of viral code it may destroy host files and starts infecting files into a PC, from there it creates a replica of itself and travels from PC to PC via external drive, the Internet, and malicious websites.

Like a biological Virus goes from one human to another and it spreads through the environment, touch, cough, etc. In the same way, a computer virus spread itself from files to files and then from one device to another. Computer virus attaches themselves to executable files and can attack into several parts of windows like the registry, services, or a specific software, some of them can attack MBR (master boot record), autorun scripts, BIOS and MS Office macros.
Overall, a virus is designed to break into your computer, destroy files and the right software, corrupt your files, make your computer completely inoperable which may lead to the complete format of your PC.
You can always make your PC safe using a good antivirus program with latest update and virus definition, always avoid suspicious files from email and rouge websites.
Worm
Worms are similar to the Virus, but a worm doesn’t need a host program to execute itself, worms are the standalone program. It uses a computer network to spread itself, and it relies on network loophole and security failure to travel from one host to another automatically and usually don’t requires user intervention. Since worms don’t require any initiation they can spread speedily across the network, infecting every PC in their path, Worms are most well know type of malware which affects more computers than a virus can.

Here are few well know worms like ILOVEYOU which transmitted through emails and cost businesses 5.5 billion US dollar in damage. The Code Red worm damaged 359,000 websites around the globe, SQL Slammer slowed down the entire web for an extended period, and the Blaster worm would force your PC to reboot continuously.
Today’s security standards make it difficult for a worm to infect user’s PC via network, but none of the security measures can guarantee that they would be able to stop any future worm. However, make sure your Firewall is on and use good security software to avoid probable worm attacks.
Trojan Horse
Trojan is another kind of malware which looks harmless, but it contains malicious code which creates a backdoor that allows your PC to be controlled remotely. The term Trojan horse came into existence from the Troy Story where the Greeks used a wooden horse to infiltrate Troy.

Unlike virus trojan doesn’t replicate itself, a trojan gets installed by users unknowingly. Once Trojan has infected your PC it can be used for different malicious purpose, like sending out spams, attacking a network or computer, DDoS attack on any website, spreading viruses, deleting files, stealing data, activating and spreading other malware.
In simple words, trojan creates backdoor which gives access to malicious users, once they are able to control your PC they can do whatever they want.
So how these Trojans can get access to your system? If you ever tried to download a crack, keygen or any program to get the full version of any software then you might get affected by such trojan, think why would anyone create a crack for software? What they are getting in return? First, they may get advertising revenue from the crack hosting sites, but such scammer has bigger goals they create trojan and attach them to cracks and keygen, once you install a crack you also install those trojans which put your computer at high risk.
So avoid using cracks, keygen or patch for any software.
Spyware
Spyware is another type of malware which collects data from your PC without your knowledge and permission, spyware runs in the background and collects your personal information like your browsing pattern, sites you visit, email, cookies, saved data into browsers, website passwords and even credit card details.

Spyware is similar to the Trojan horse in that users unknowingly install the product when they install some other software or freeware. Spyware exists as an independent program then can track your keystrokes, snoop on other files, change your default homepage, monitor your activity, stealing your personal information and send back them to the creators. Your data can be used in several malicious ways which include selling your data, targeted advertising, scams, spam or identity theft.
Adware
Adware is a bit different from spyware the primary intent of adware is to show different advertisements, pop-up window, flash ads, links to rogue websites, redirecting to different links, change homepage and default search engine, slows down browsing speed, causes frequent browser crash.

Adware monitors your browsing pattern, cookies, interest and sends them back to the creators where they re-target the users with relevant ads; technically adware is not a virus.
Whenever you install freeware these adware comes along with them; these are sponsored programs which make the main program free to use in exchange of ads when you uninstall the free program the ads will stop running on your computer.
Adware is considered as a legitimate alternative to the consumers who don’t want to pay for the software, games, programs and other free utilities. But sometimes we mistakenly install many Adware at the same time which becomes annoying, and some of them are tricky to remove.
Scareware
Scareware is another type of malware that uses social engineering to cause shock, anxiety or perception of threat and trick users to buy unwanted and potentially dangerous software.
Scareware generates pop-ups which resemble Windows system messages like particular error message saying there are problems found in your PC, registry error found, Computer at serious risk, virus found, etc. These pop-up messages are designed in a way which looks like they come from user’s operating system when they are actually a web page.
Scareware tricks users to download or buy fake antivirus, a firewall application, registry cleaner or a PC optimizer, usually a rogue software which has minimal to no use. This scareware may generate continuous pop-ups saying “Your Computer is infected with spyware or malware click here to fix it” now if a user clicks on any of such buttons they may end up installing rogue software which itself may be a malware.
Best practice to stay away from scareware is to ignore every popup saying such lame things while surfing the web, and do not click here and there on such pages. Scareware spreads by malvertising where a genuine ad company gets tricked by the advertiser which leads into spreading scareware.
Ransomware
Ransomware is a type of malware which prevents users from accessing their system. Ransomware locks down the system and asks for ransom through certain online payment methods in order to unlock the user’s computer.

Some of the ransomware encrypt files in the system hard drive, which makes it very hard to decrypt the data without the encryption key, paying ransom to the creator may or may not provide you the encryption key like crypto locker which encrypts individual files and folder.
Some ransomware only locks the system and do not encrypt the user’s data; such ransomware can be removed easily by a tech savvy user by booting the Windows computer in safe mode or using bootable antivirus disk.
Ransomware can affect MBR (Master boot record) which makes is tough to boot into the system without paying the ransom. However, there is no guarantee that they will unlock the system after paying the ransom, one of the famous ransomware was FBI Moneypak, which locks the system and asks for payment, it was widely spread into the US and Canada in 2012-2014.
Ransomware spread through trojans, scareware, email attachments, infected and pirated programs and from compromised websites and threaten users that they have been involved in illegal activities and pretend to be some legal entities.
Rootkit
A rootkit is a software or set of application typically malicious that enables administrator-level access to a computer or computer network. Rootkit get activated every time you boot into operating system since they activated before an operating system gets completely booted up which makes it very hard to detect by antivirus.
Rootkit can get to a computer by a Trojan, suspicious email attachments or by compromised websites after getting user level access to the system either by breaking a password or by exploiting any vulnerability into the system. Once a rootkit is installed it allows the installation of hidden files, hidden user accounts, processes and attackers can mask intrusion and get root access to the system.
A rootkit can monitor traffic, keystrokes, can create a backdoor for malicious usages by hackers, and it can remove installed programs and security suits in order to prevent the detection.
Bots
The bot is a short name for “robot” and is an automated process/script which interacts with other computer or network services; bot is a software program which automates different tasks over the Internet using specially written scripts.
 A web bot can be utilized for both good and malicious intent, a good bot is responsible for crawling the web like Google search bot, but a malicious bot is a self-propagating malware which infects a host computer and connects back it to the central server. The central server is called “botnet” which connects with the several host computers using a bot,
A web bot can be utilized for both good and malicious intent, a good bot is responsible for crawling the web like Google search bot, but a malicious bot is a self-propagating malware which infects a host computer and connects back it to the central server. The central server is called “botnet” which connects with the several host computers using a bot,
The central server is called “botnet” which connects with the several host computers using a bot, botnet can command every host computer for the different malicious purpose like denial-of-service attack, spreading malware, keystroke monitoring, spreading spams, collect passwords, gather financial information or generating massive traffic using host computers.
Bots do not work alone, once the army of bot affects the large number of computer they can be controlled by a master computer called command and control server and attackers can instructs them to work on their behalf using the master computer.
Vulnerability
Humans are prone to make mistakes which may lead to serious flaws. A computer vulnerability is a flaw in the software, operating system or service occurs by programming errors which allow cyber criminals to attack the system. Vulnerability leaves it open to the potential for exploitation in the form of unauthorized access or malicious behavior such as viruses, worms, Trojan horses, bots, ransomware, and other forms of malware.

Vulnerability consists of 3 main parts, a system flaw, attackers access to the flaw and capability to exploit the flaw in a system. First, an attacker finds the holes in a software of operating system then get the access to that security hole and then delivers malicious codes.
Exploit
Exploits take advantage of a particular vulnerability in the system, exploits in computer security refers to a piece of software or a sequence of commands that take advantage of vulnerability to carry out some form of malicious intent, such as Trojan horses, denial-of-service attack, worms or viruses.
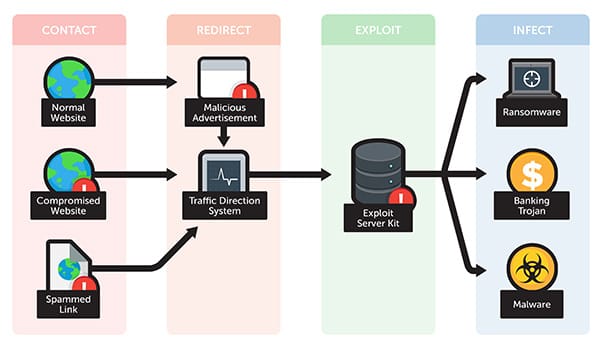
When the vendor of software or operating system finds that an exploit is taking advantage of weakness in their software/OS, they issue a fix or patch in response. The user needs to update their software or Operating system to make it secure against the exploit. Failing to install a patch or fix for a given problem exposes the user to a security breach.
Combating Virus, Worms Trojan, Adware, Spyware, Ransomware, etc
Now you have a clear idea about the different type of malware, and what they can do to your computer, it is advised that always install a good antivirus which has high detection rate and can provide you protection from all known threat and should be able to block unknown threats also.
Never install any kind of crack keygen or pirated software, beware while visiting torrent, porn, gambling and other sensitive sites. Always keep your system updated with latest security patches and make sure the firewall is turned ON. While installing freeware keep an eye on what else they are offering apart from main software, do not click next and next too fast during installation.
Also Read-
- 10 Best Free Antivirus for Windows 7, 8 & 10 in 2016.
- Things to Know Before Buying Best Antivirus Software.
Definition from Wikipedia.org/wiki & Damage data by worms from lifehacker.com